See Recon Agent in Action
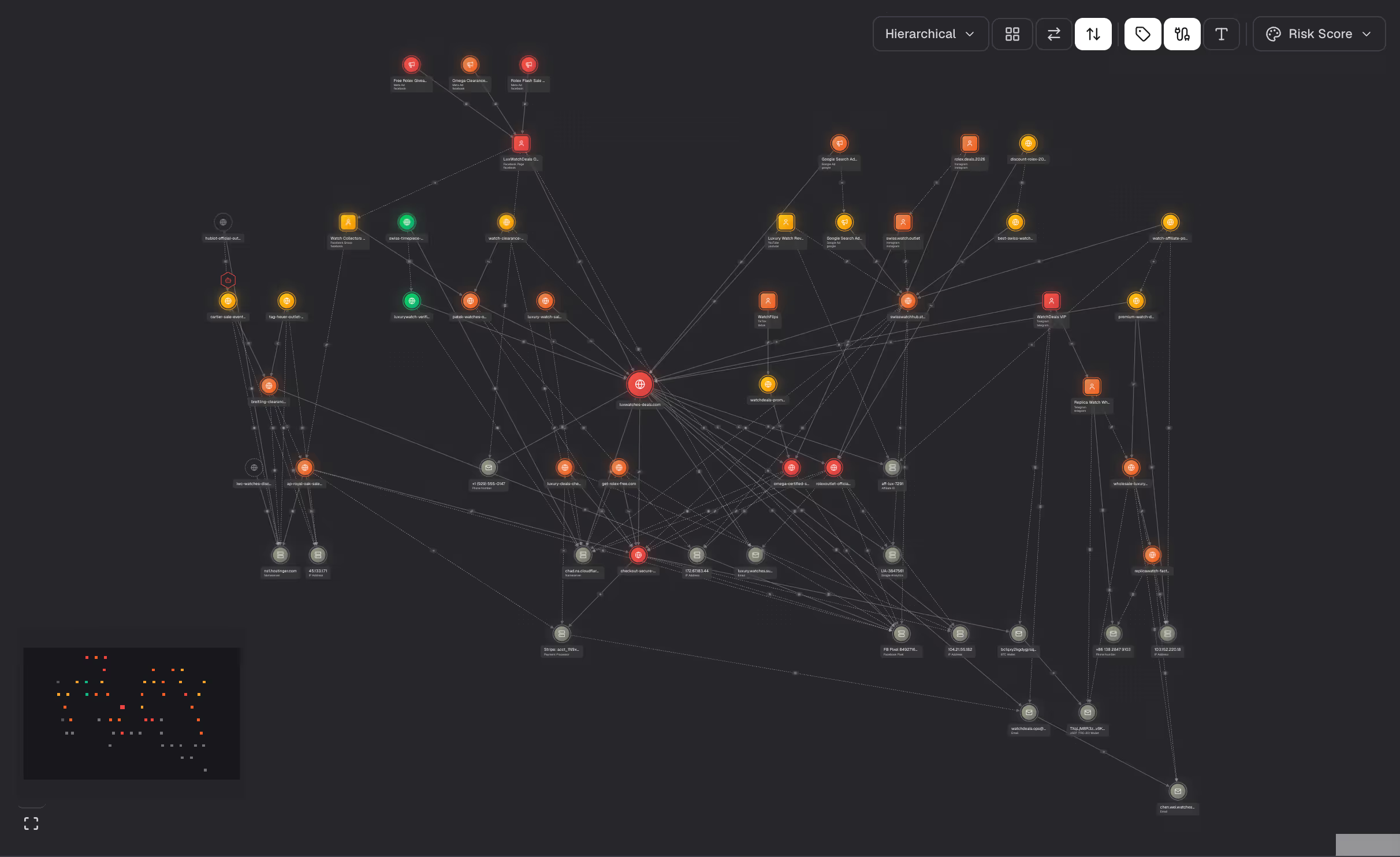
Trace to source
Follow any signal through ownership, hosting, and operational layers. Find where the threat actually started.
Map the full network
One signal expands into the complete adversarial system. Operators, infrastructure, pre-staged assets, all linked.
Surface attacks before they launch
Recon detects pre-staged infrastructure, assets created but not yet activated, so teams intercept before victims are reached.

.svg)
.svg)




