
How Recon Agent Works
One agentic process. Five capabilities that transform signal into operation.

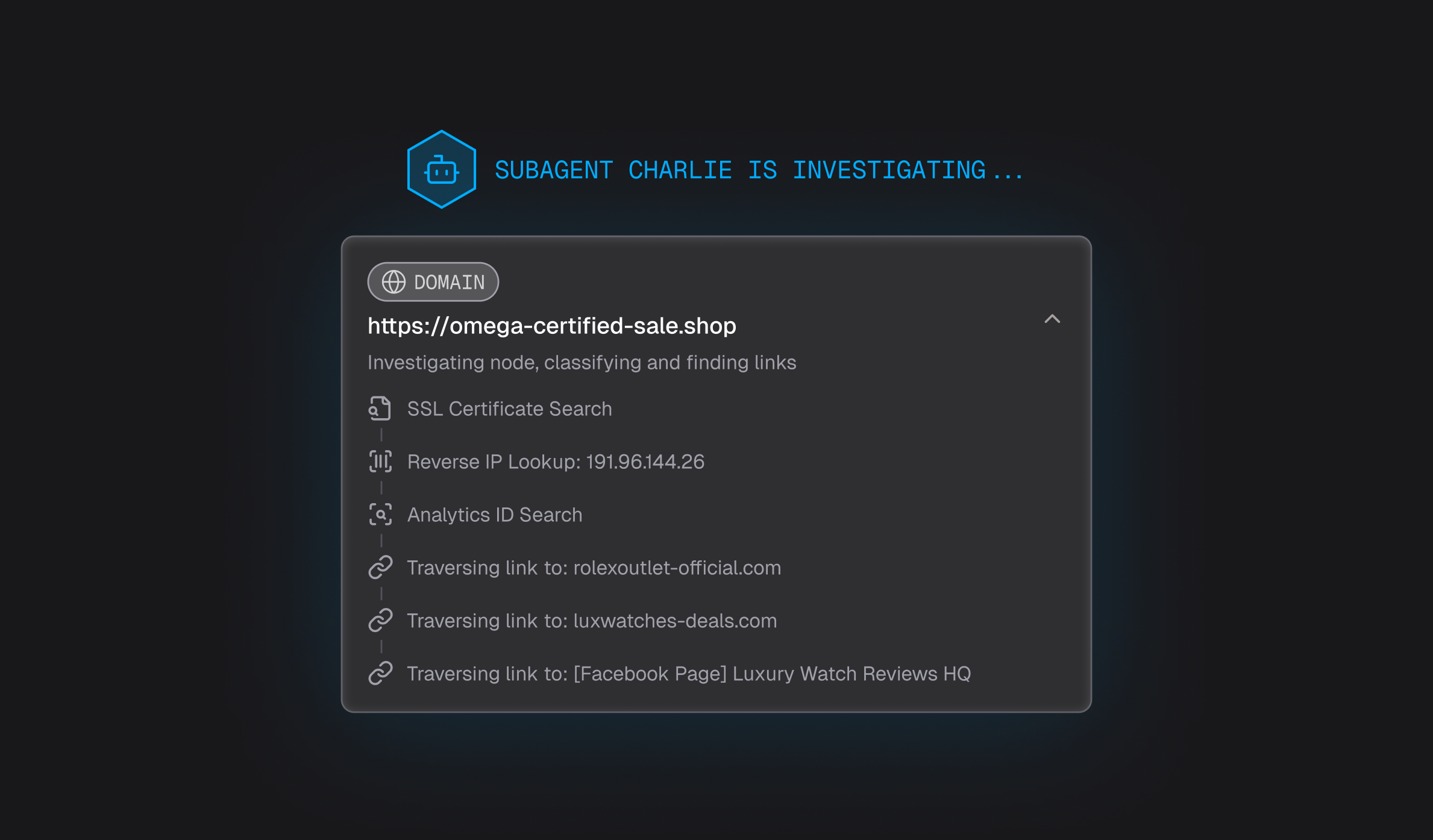
1. Trace to the Source
Follow any signal through ownership, hosting, and operational layers to identify its originating entity and root source. Understand where the threat began, not just where it surfaced.

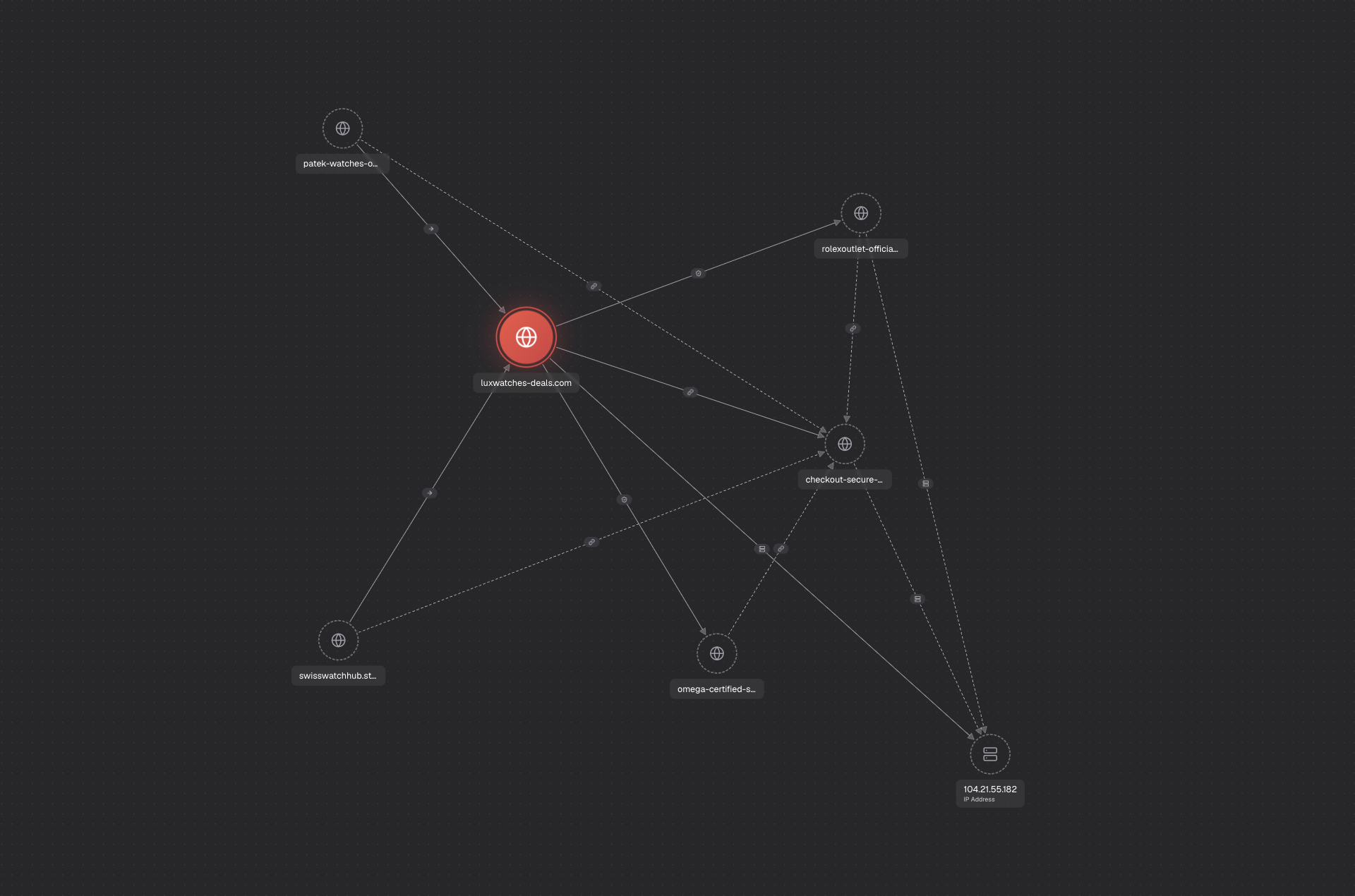
2. Expand Across Relationships
Traverse laterally across shared infrastructure and connections to uncover all related entities, assets, and supporting systems. One signal becomes a complete network map.
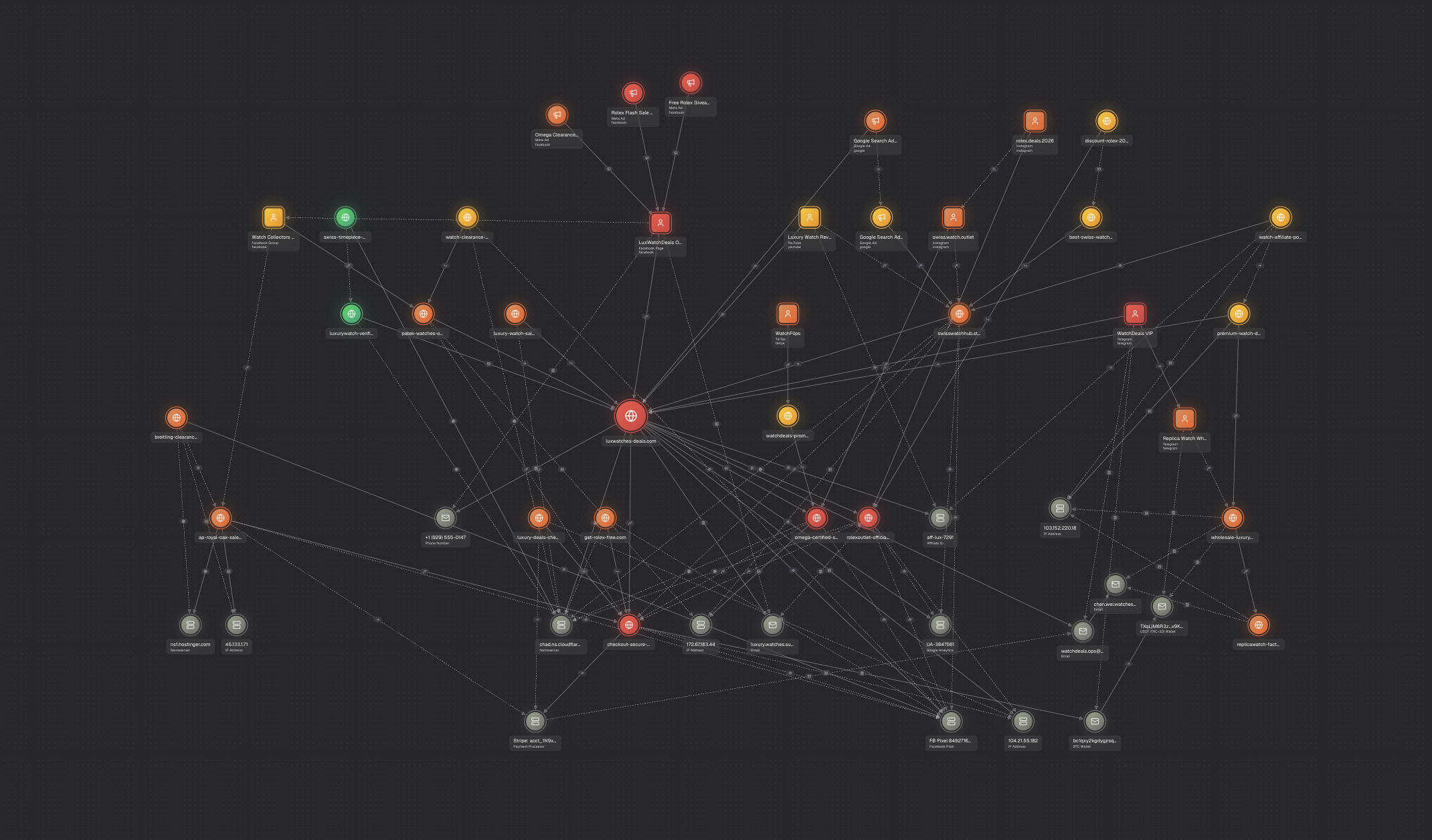

3. Map the Full Hierarchy
Build a structured, visual graph of parent, peer, and child relationships across entities, infrastructure, and activity. Complex coordinated systems become immediately understandable at a glance.

4. Expose the Operation
Surface the operators, organizations, and coordinated networks behind the activity — including the tactics, infrastructure, and channels used to scale. This transforms investigation into attribution.
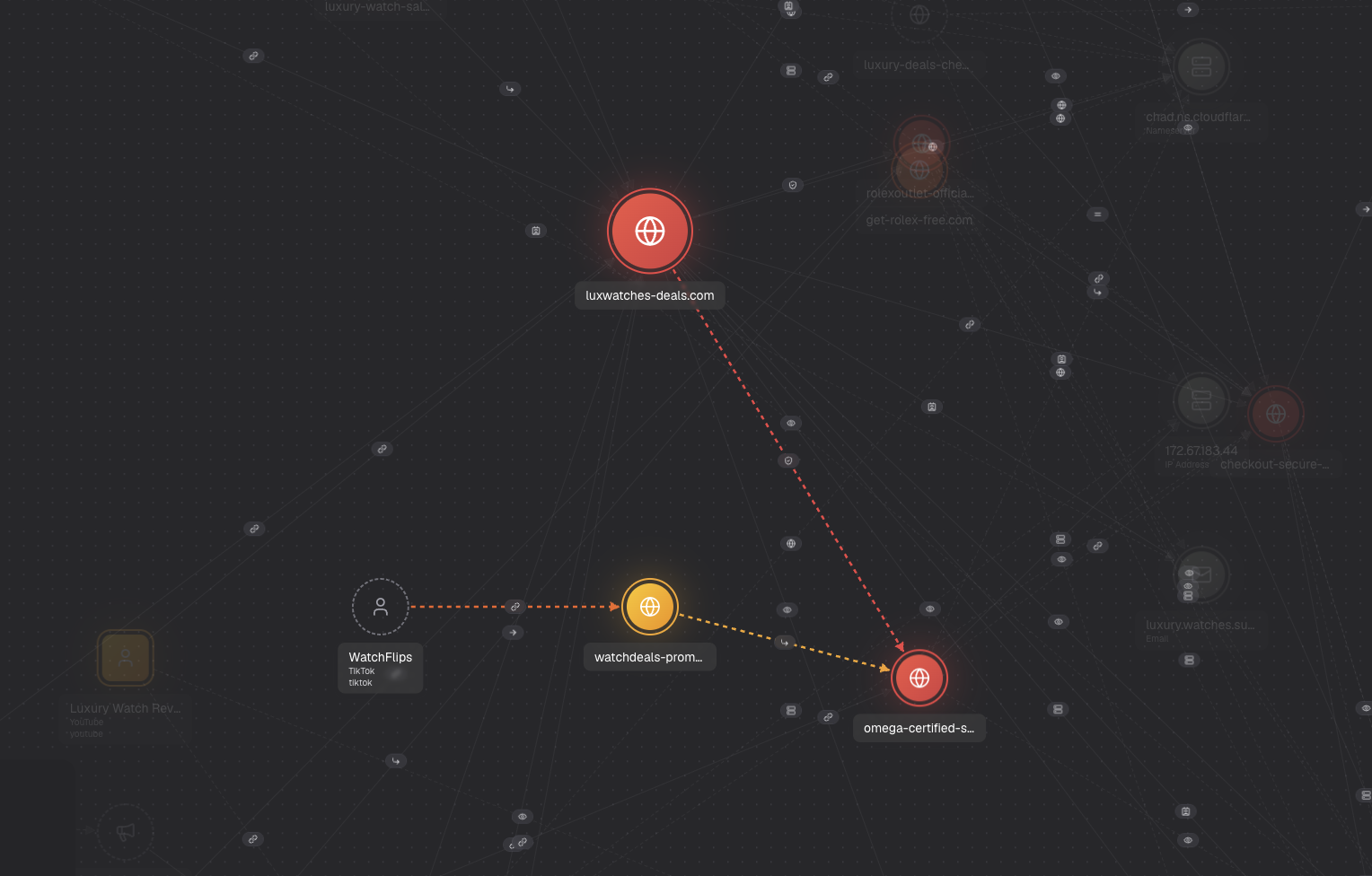

5. Enable Attribution and dismantle
Provide complete, high-confidence context so teams can attribute activity to specific operators and act strategically against entire operations, not individual artifacts. The difference between cutting a branch and pulling a root.









