Product Security
From trial credit harvest to grey market storefronts, Outtake maps the full operation and shuts it down before customers see it.

Use cases
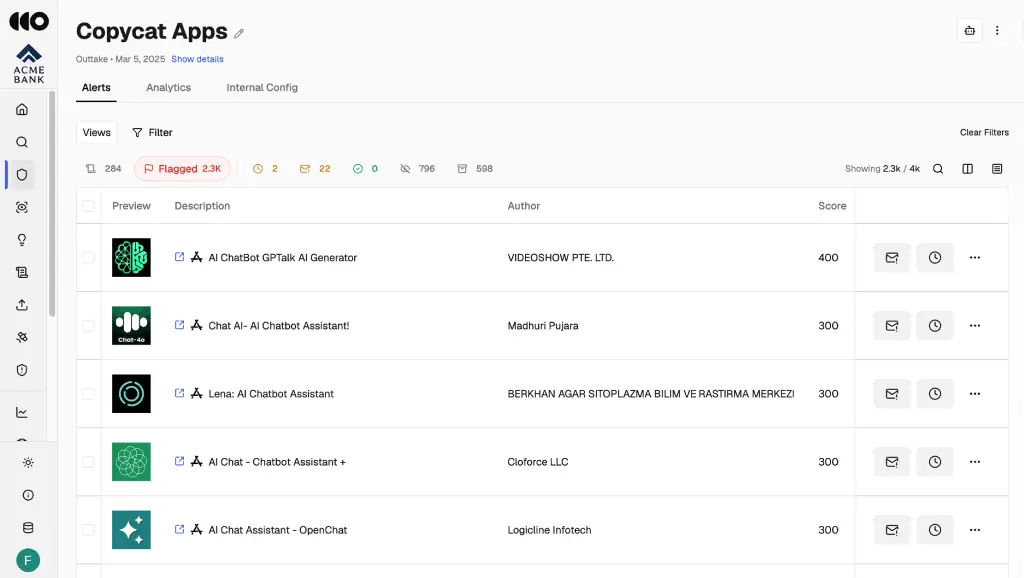
Unauthorized Resale & Grey Market Storefronts
Dismantle the operation behind every grey market listing, not just the storefront.
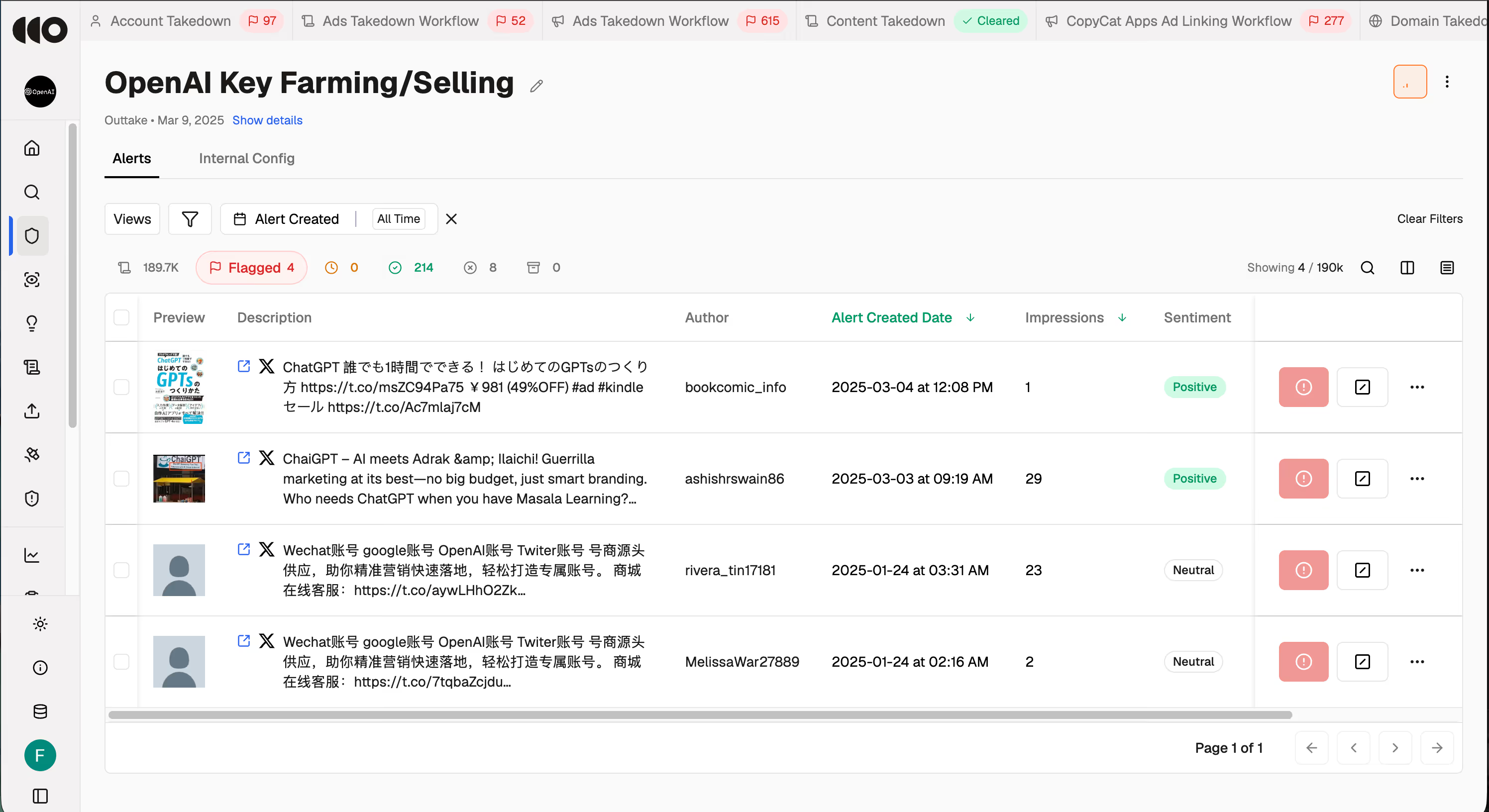
Free-Tier and Trial Credit Abuse
Spot the harvest pattern on day one, not after thousands of credits are gone.
Brand Damage from Fraudulent Access
Catch abuse before customers see it, not after support tickets pile up
How it works
Move from a single unauthorized listing to a complete map of the resale network behind it.

Surface Detection
You Define What Is Being Abused – Free tiers, trial programs, paid plans, access channels, partner ecosystems. Outtake learns your full product surface in minutes and knows exactly where revenue is leaking
Proactive Detection
Before the Customer Complaint – Most vendors find out about unauthorized resale the same way their customers do. Outtake monitors continuously across visual brand usage, pricing patterns, and infrastructure signals, catching what keyword tools miss before the first complaint lands
Network Dismantlement
Not Storefront Whac-A-Mole – Reactive takedowns clear individual listings while the infrastructure behind them keeps generating new ones. Outtake maps and dismantles the entire operation at once.

Detection Beyond Keywords
Context, Visual, and Infrastructure Signals – Unauthorized resellers don't always use your brand name. Outtake analyzes visual brand usage, pricing patterns, and infrastructure signals to catch what keyword tools miss.
See Product Protection in action
See how we take a single unauthorized listing, map the operator network behind it, and take down every connected storefront. Resale rings. Harvested credits. Cloned accounts. Before customers see it.

Here's what our clients are saying
“Some of these matters have been lingering since 2024. Strong results here means huge value we can relate back to the business.”

“We demo a lot of platforms in this space and most are painfully complicated. Outtake is by far the most user friendly.”

“What took my analyst a full day, your platform finished in five minutes. I cannot think of enough good adjectives for this.”

FAQs
Related resources

AppLovin
Fending off modern social engineering attacks during moments of peak publicity
Always-on protection that finds and zaps digital impersonation before it causes real harm

CashApp
Fighting fraud on video-first platforms without scalable coverage
Detection that mirrors how analysts think without needing to watch every video manually

